If you’ve ever opened a verified contract on Etherscan and felt overwhelmed, you’re not alone. Learning how to read a smart contract is like learning a new language—except the stakes involve money, governance power, and on-chain reputation. This guide distills a battle-tested, step-by-step process you can use today, whether you’re a builder, investor, auditor, or power user.
TL;DR
– Start with the contract’s context: What does it do, who can call it, and where are the funds?
– Map state variables, roles, and permissions first.
– Read public/external functions next, track effects and interactions, and watch for external calls.
– Check upgradeability, proxies, and libraries.
– Verify assumptions by simulating transactions and reading event logs.
Why learning How to Read a Smart Contract matters
- Capital safety: Spot reentrancy, improper access control, unchecked external calls, and broken math before you click “confirm.”
- Governance clarity: Understand who can pause, mint, upgrade, seize collateral, or change fees.
- Builder velocity: Read proven patterns instead of reinventing wheels.
- Due diligence: Evaluate protocols instead of relying on social proof.
Reading code isn’t just for auditors—DeFi participants, NFT traders, and DAO voters all benefit. The difference between a confident on-chain decision and a costly mistake often comes down to how well you can parse a contract’s surface area.
The 10-minute blueprint for reading any Solidity contract
1) Establish context
– Find the verified contract on a reputable explorer (e.g., Etherscan, Arbiscan, Basescan).
– Read the “Contract” tab summary, compiler version, license, and verification status.
– On the “Read Contract” tab, inspect public variables—especially owner, admin, pendingAdmin, treasury, feeRecipient, and token addresses.
– On the “Transactions” tab, look at recent interactions to understand typical usage.
2) Identify entry points and permissions
– Scan for Ownable, AccessControl, or custom role systems (e.g., DEFAULTADMINROLE, MINTER_ROLE).
– Track modifiers like onlyOwner, onlyRole, whenNotPaused, nonReentrant.
– Create a small map: who can do what? Mint? Upgrade? Withdraw? Pause?
3) Map state and storage
– List key state variables (balances, reserves, collateral, totalSupply, fee settings, price feeds, oracles).
– Note mappings and nested mappings; e.g., mapping(address => mapping(address => uint256)) allowances.
– Highlight constants and immutables; they often define unchangeable parameters.
4) Constructor or initializer
– For non-upgradeable contracts, the constructor sets critical defaults.
– For proxies, find initialize functions and versions (e.g., initializer, reinitializer). Search for UUPS or TransparentUpgradeableProxy patterns.
5) Public and external functions
– Read function signatures and docstrings (if any).
– Apply Checks–Effects–Interactions (CEI) mentally:
– Checks: require, revert conditions, role checks, nonReentrant
– Effects: internal state writes
– Interactions: external calls, token transfers, oracles
– Note event emissions that confirm state transitions.
6) External calls and libraries
– Seek calls to other contracts (token.transfer, router.swap, oracle.latestAnswer, pool.flashLoan).
– Watch for delegatecall, call, callcode, staticcall; these change trust and attack surface.
– Inspect libraries (SafeERC20, SafeMath pre-0.8, custom math, interest rate models) and their assumptions.
7) Upgrades, pausing, and killswitches
– Does the contract use a proxy? Check the proxy admin, implementation address, and upgrade functions.
– Identify emergency stops (pause/unpause) and recovery flows.
– Confirm who controls upgrades and rescues.
8) Invariants and accounting
– Track balance-related invariants: totalSupply = sum(balances), reserve = deposits − borrows, or fee math.
– Look for unchecked blocks in Solidity >= 0.8; make sure they’re intentional for gas, not a logic hole.
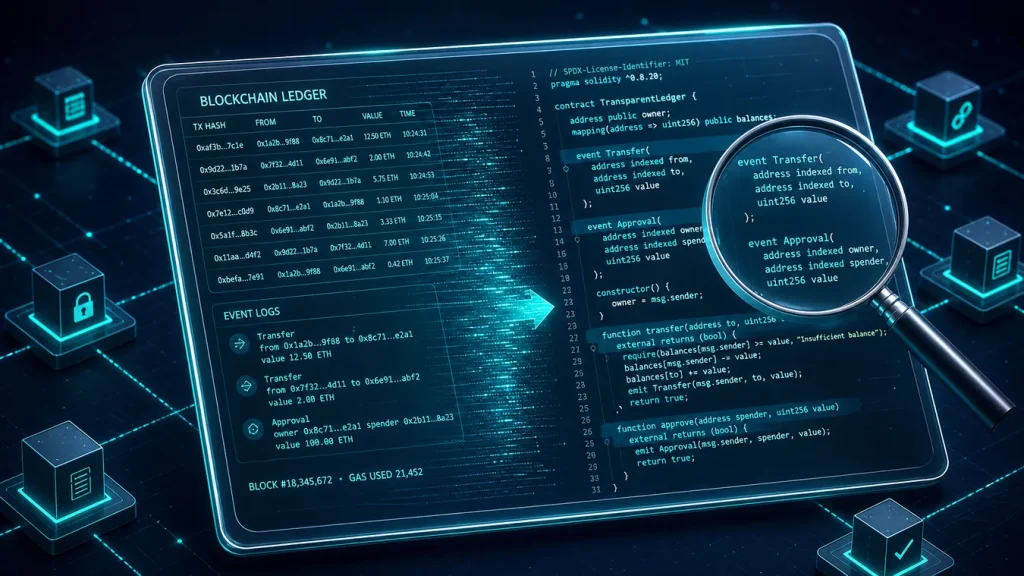
9) Event logs and off-chain consumers
– Events define the public audit trail. Correlate events with function logic.
– If a function changes state but emits nothing, consider how off-chain indexers will know.
10) Validate through simulation
– Replay recent transactions in a simulator (e.g., Tenderly) and inspect traces.
– Write a minimal test in Foundry/Hardhat to confirm a hypothesis before acting on-chain.
Where the code hides: explorers, repos, and proxies
- Explorers: Start with verified source code and ABI. If unverified, consider risk elevated.
- Repos: Many teams publish on GitHub. Confirm the commit matches the deployed bytecode.
- Proxies: If the address is a proxy, open the implementation address. On Etherscan, the “Read as Proxy” or “Write as Proxy” tabs help. Always locate the implementation before drawing conclusions.
Pro tip: Paste the contract address into OpenZeppelin’s Upgrades Plugins docs tooling or use their CLI to inspect storage layout when relevant.
A compact walkthrough on a familiar pattern (ERC-20 with roles)
Below is a simplified, annotated snippet that illustrates how you might read an ERC-20 variant with minting and pausing. Focus on comments that mirror a reading process.
“`solidity
// SPDX-License-Identifier: MIT
pragma solidity ^0.8.20;
import “@openzeppelin/contracts/token/ERC20/ERC20.sol”;
import “@openzeppelin/contracts/access/AccessControl.sol”;
import “@openzeppelin/contracts/security/Pausable.sol”;
contract ExampleToken is ERC20, AccessControl, Pausable {
bytes32 public constant MINTERROLE = keccak256(“MINTERROLE”);
constructor ERC20("ExampleToken", "EXT") {
_grantRole(DEFAULT_ADMIN_ROLE, msg.sender); // who controls roles
_grantRole(MINTER_ROLE, msg.sender); // who can mint
}
function pause external onlyRole(DEFAULT_ADMIN_ROLE) { _pause; }
function unpause external onlyRole(DEFAULT_ADMIN_ROLE) { _unpause; }
function mint(address to, uint256 amount) external onlyRole(MINTER_ROLE) {
_mint(to, amount);
}
function _beforeTokenTransfer(
address from,
address to,
uint256 amount
) internal override {
require(!paused, "paused"); // transfers blocked during pause
super._beforeTokenTransfer(from, to, amount);
}
}
“`
How to read it quickly:
– Roles: DEFAULTADMINROLE can grant/revoke; MINTER_ROLE can mint. Ask: who holds these today? Any multisig?
– Pausing: Transfers revert when paused. Who can pause? What’s the social policy for using it?
– Supply policy: Unlimited mint is powerful; verify off-chain governance or a time-lock.
– Events: Check if role changes and mints emit events (OpenZeppelin does). Indexers rely on those logs.
Common red flags and how to spot them fast
- Reentrancy pathways
- Look for external calls before state updates or missing nonReentrant modifier.
- Pay attention to ERC-777 or callback-capable tokens.
- Missing or weak access control
- Admin-only functions that are public or missing modifiers.
- Misconfigured roles or self-revoking defenses that brick upgrades.
- Dangerous delegatecall or selfdestruct
- Delegating to untrusted addresses can hand over storage control.
- selfdestruct can nuke logic or break invariants.
- Price oracle assumptions
- Stale prices, manipulable TWAPs, direct AMM reads without smoothing.
- Signature malleability and replay
- Verify EIP-712 domain separators and nonces.
- Unclear upgrade flows
- Proxy admin keys on EOAs instead of multisigs or timelocks.
- Accounting drift
- Fees or rebases that make totalSupply drift from expectations.
- Front-running/opportunistic MEV
- Think about who sees the transaction first and what they can do.
Tools that speed up your reading
- Explorer suites: Etherscan/Arbiscan/Basescan “Read/Write” tabs, Proxy introspection.
- Slither: Static analysis and quick vulnerability hints (Slither).
- Foundry: Fast tests and scripts (Foundry Book).
- Tenderly: Transaction traces, gas profiling, event insights .
- OpenZeppelin Contracts: Reference for secure primitives (OpenZeppelin).
Workflow example:
1) Download sources from explorer.
2) Run Slither for a first-pass smell test.
3) With Foundry, write 2–3 minimal tests that hit the riskiest functions.
4) Simulate a recent mainnet transaction to confirm your mental model.
ABI, selectors, and what the chain actually sees
- ABI: Defines how function names and parameter types map to 4-byte selectors.
- Selector collisions: Rare but possible; be mindful when you see low-level call usage.
- Event topics: The first topic is the keccak hash of the event signature; indexed params appear in topics, others in data.
Quick trick: If you only have a transaction input and no verified source, use a decoder (Etherscan, 4byte.directory, or Foundry’s cast) to guess the function.
Reading upgradeable contracts like a professional
- Transparent proxy pattern: Admin-only calls go to the proxy; users hit the implementation.
- UUPS: The implementation carries the upgrade logic; require precise access checks.
- Storage gaps: Preserving layout across versions avoids storage collisions.
- Initializers: Ensure they can’t be re-run. Look for initializer modifiers and versioned reinitializers.
Always confirm:
– Who is ProxyAdmin?
– Can they change implementation unilaterally?
– Are upgrades gated by a timelock or multisig with a clear process?
Gas, griefing, and UX gotchas
- Unbounded loops over dynamic arrays can fail under block gas limit.
- ERC-20 non-standard tokens (returning no bool) require SafeERC20 wrappers.
- Pull vs. push payments: Pull patterns reduce reentrancy and stuck funds.
- Pausable systems: Don’t just check pause flags—evaluate who triggers them and when.
Practice: a quick reading checklist you can reuse
- Context
- What problem does this contract solve? Where does value sit?
- Trust and roles
- Who can mint/upgrade/pause/change fees?
- State and storage
- Which variables define balances, reserves, and limits?
- Core functions
- Inputs, checks, effects, interactions, events.
- External calls
- To which contracts? Safe? Checked returns? Reentrancy protected?
- Upgradeability
- Proxy type, admin, initializer protection, storage layout.
- Failure modes
- How do things break? Can users exit? Are there caps and circuit breakers?
Make it a habit: write a 5–10 line summary of any contract you review. Your future self will thank you.
Funding your research and testing
To try interactions on mainnet or L2s, you’ll need gas and sometimes collateral assets. If you’re moving between centralized and decentralized rails, consider fees and security.
- On-ramp/off-ramp: Use reputable exchanges for fiat conversion and quick withdrawals.
- Network awareness: Gas on Ethereum mainnet vs. cheaper L2s like Arbitrum, Base, Optimism.
- Wallet hygiene: Dedicated research wallet, hardware signing for high-value moves.
If you need an exchange account, you can register through this offer:
– 20% fee discount and up to $10,000 in benefits when you sign up on Join Binance with code CRYPTONEWER. Enter the referral code CRYPTONEWER during registration to qualify. Lower trading fees mean more budget for on-chain experiments and simulations.
Example workflow: from zero to insight in 30 minutes
1) Pick a protocol and grab the primary contract address from official docs.
2) On Etherscan, confirm it’s verified and check the proxy status.
3) Identify admin keys and roles; map them to multisigs or EOAs.
4) Skim state variables, then read the two most-called external functions.
5) Trace a fresh transaction in Tenderly and confirm the event sequence.
6) Draft a 10-line risk memo: trust model, upgrade risks, reentrancy surface, oracle dependencies.
7) (Optional) Write a Foundry test to emulate the riskiest path you saw.
Repeat this across a few protocols. You’ll quickly build intuition for patterns that are safe, risky, or just unusual.
Smart contract reading patterns you’ll encounter again and again
- Governance modules: Proposals, queues, timelocks, executors. Confirm delays and cancellation logic.
- AMMs/DEXes: Invariant math (x*y=k or concentrated liquidity), fee accrual, and oracle windows.
- Lending markets: Collateral factor, liquidation incentives, interest accrual, reserve management.
- Bridges/wrappers: Lock-and-mint vs. burn-and-release; verify guardians, relayers, and threshold signatures.
- NFT drops: Mint windows, allowlists, per-wallet caps, reveal mechanics.
In each pattern, ask two meta-questions: What are the explicit permissions, and what are the implicit assumptions? Many exploits target the latter.
Quick reference: terminology that unlocks understanding
- CEI: Checks–Effects–Interactions pattern to reduce reentrancy risk.
- View/pure: Read-only vs. no-state/no-call functions; safe to call off-chain.
- nonReentrant: Mutex-style modifier that blocks nested calls.
- delegatecall: Execute code in the context of the caller’s storage; powerful and dangerous.
- Oracle: An external data feed; trust boundary alert.
- Revert reasons: Human-readable breadcrumbs for failure paths.
Keep sharpening the edge
- Read one mature protocol per week; compare patterns across versions.
- Track disclosures and post-mortems; translate incidents into your checklist.
- Contribute minimal PRs or tests to open-source repos; it cements understanding.
Resources to keep handy:
– Solidity Docs
– Ethereum Yellow Paper (for the brave)
– OpenZeppelin Contracts
–
–
– Foundry
Bonus: a handy funding and fees tip for frequent testers
If you plan to bounce between chains, pay for gas, and test interactions often, trading fees add up quickly. To reduce overhead and keep more of your budget for experiments:
- Sign up for Join Binance with code CRYPTONEWER to get a 20% fee discount and up to $10,000 in extra benefits. Use referral code CRYPTONEWER at registration.
- Withdraw directly to the chain you’re testing to avoid extra bridges when possible.
- Keep a small working balance on L2s to iterate faster without mainnet gas shock.