If you’ve ever copied a “transaction hash” into a block explorer, you’ve already used hashing. So, what is hashing in blockchain, really? In plain terms, a hash is a short, fixed-length fingerprint of any data. In blockchain systems, that fingerprint anchors trust: it links blocks, identifies transactions, powers consensus, and lets anyone verify data integrity without revealing the original data.
Hashing sits at the heart of Bitcoin, Ethereum, and most distributed ledgers. It’s the difference between a ledger you can independently verify and one you merely have to trust. This post breaks down how hashing works, where it’s used, and how to reason about its security properties—without hand-waving.
The one-minute answer
- A cryptographic hash function takes any input and returns a fixed-size output (the “digest”).
- Tiny changes in input create radically different outputs (the avalanche effect).
- It’s designed to be one-way: given a hash, you can’t feasibly recover the input.
- In blockchain, hashes link blocks, identify transactions, compress large datasets into Merkle roots, and enable proof-of-work.
How hashing works under the hood
A good cryptographic hash function (like SHA-256 or Keccak-256) mixes input bits through multiple rounds of permutations and non-linear operations. The result is:
- Deterministic: same input → same output, every time.
- Fixed length: SHA-256 always outputs 256-bit values, no matter if the input is one byte or a gigabyte.
- Avalanche effect: flip one bit in the input and roughly half the output bits should flip.
- Preimage resistance: given H(x), it’s computationally infeasible to find x.
- Second preimage resistance: given x, it’s infeasible to find x′ ≠ x with H(x′) = H(x).
- Collision resistance: it’s infeasible to find any x ≠ y with H(x) = H(y).
These properties make hashes ideal for verifying integrity and building tamper-evident data structures.
Quick demo you can try
Hash the string “hello” with SHA-256 and you’ll get:
- SHA-256(“hello”) = 2cf24dba5fb0a30e26e83b2ac5b9e29e1b161e5c1fa7425e73043362938b9824
- SHA-256(“Hello”) = 185f8db32271fe25f561a6fc938b2e264306ec304eda518007d1764826381969
A single capital letter completely changes the digest.
Code snippets to experiment:
“`python
Python 3
import hashlib
print(hashlib.sha256(b”hello”).hexdigest())
“`
javascript
// Node.js
const crypto = require('crypto');
console.log(crypto.createHash('sha256').update('hello').digest('hex'));
Where hashing appears in blockchain systems
1) Transaction identifiers (txids)
- In Bitcoin, a transaction’s ID is a double SHA-256 hash of its serialized bytes. Wallets and block explorers use this digest to reference the transaction.
- On Ethereum, transaction hashes use keccak-256 (often called SHA3 in the ecosystem, although the exact standard SHA-3 differs slightly from Ethereum’s keccak variant).
Why double hashing in Bitcoin? It’s a historical design choice that helps reduce certain parsing ambiguities and protects against length-extension quirks in Merkle constructions.
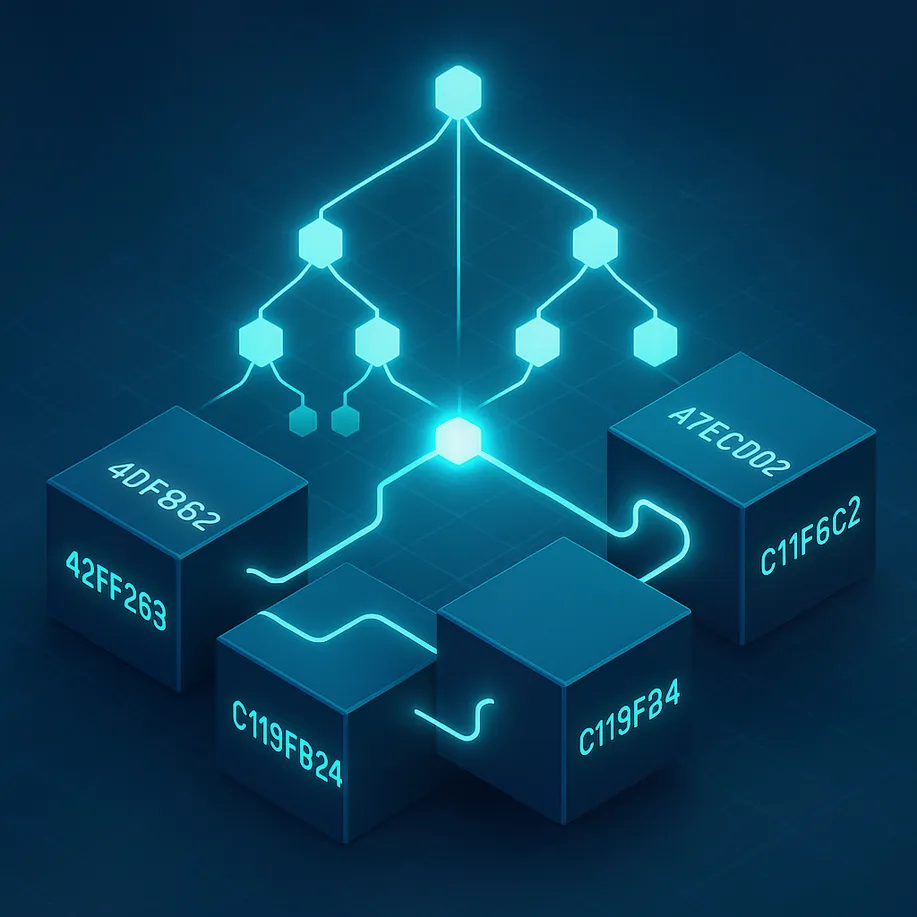
2) Merkle trees and Merkle roots
Blockchains compress a block’s transactions into a single 32-byte summary called a Merkle root:
– Pairwise hash transactions to form parent nodes.
– Keep hashing pairs up the tree.
– The top node is the Merkle root, stored in the block header.
Light clients (like mobile wallets) can verify a transaction is included in a block using a short Merkle proof rather than downloading the entire block. This is the backbone of SPV (Simplified Payment Verification).
3) Block headers and linking
Every block header contains the hash of the previous block, the Merkle root, a timestamp, a nonce, and other fields. The block’s own ID is the hash of its header. Altering any transaction would change the Merkle root, which changes the block hash, breaking the chain. This chained hashing makes tampering obvious and expensive.
4) Proof of Work (PoW)
Miners in PoW networks repeatedly hash candidate block headers while changing a nonce to find an output below a network-defined target. Because hashes are unpredictable, the only strategy is trial and error at scale. The “hash rate” is a measure of how many attempts the network can make per second.
5) Proof of Stake (PoS) still needs hashing
Even without mining, PoS chains rely on hashing to build Merkle trees, compute state roots, derive randomness, and authenticate data in light clients. Hashing is a foundational primitive regardless of consensus.
6) Address derivation and smart contracts
- Ethereum addresses are the last 20 bytes of the keccak-256 hash of a public key.
- Solidity’s keccak256 is frequently used to derive unique identifiers, map keys, and EIP-712 typed data hashes.
- Log topics, Bloom filters, and various protocol-level commitments rely on hashing.
Hashing vs encryption vs digital signatures
These terms often get conflated:
– Hashing: one-way, fixed-length fingerprint; verifies integrity but doesn’t hide content.
– Encryption: two-way; hides content so only those with keys can read it.
– Digital signatures: prove authorship/consent over specific data, often by signing a hash of that data.
In practice, protocols sign hashes because they are fixed-size and unambiguous. You validate a signature against the same hashed message.
Security properties that actually matter
- Collision resistance isn’t absolute—collisions exist mathematically—but a good function makes finding one astronomically expensive. For 256-bit hashes, brute-force collision search is about 2^128 operations (birthday bound).
- Preimage resistance for 256-bit output is about 2^256 work. That’s far beyond any feasible computation today.
- Length-extension: certain hash constructions (like Merkle–Damgård) have quirks; designers use domain separation, padding, or double hashing to avoid pitfalls.
For developers, the takeaway is simple: use modern, vetted functions; never invent your own; and avoid rolling custom constructions unless you fully understand the cryptographic assumptions.
Bitcoin, Ethereum, and the algorithms you’ll see
- SHA-256: Bitcoin’s workhorse. Transactions are double-SHA-256’d; block headers are hashed; mining targets these outputs.
- Keccak-256: Ethereum’s variant often casually called SHA3. Used for addresses, logs, and the EVM’s SHA3 opcode (now called KECCAK256). Standardized SHA-3 (FIPS 202) differs slightly; Ethereum kept the pre-standardization keccak.
- Others: Some modern chains and applications consider BLAKE2 or BLAKE3 for faster throughput while keeping strong security properties.
Useful references:
– Bitcoin whitepaper by Satoshi Nakamoto: bitcoin.org/bitcoin.pdf
– NIST SHA-3 standardization: csrc.nist.gov
– Ethereum keccak notes: ethereum.org
Merkle proofs in a nutshell
A Merkle proof for a transaction contains the siblings along the path from the leaf to the root. To verify:
1) Hash the transaction to get the leaf.
2) Iteratively hash it with each sibling (in the correct order and concatenation direction).
3) Check the result equals the block’s Merkle root.
If the root matches the header’s commitment—and the header is in a sufficiently deep chain—your light client can trust inclusion without seeing the entire block.
Hash rate, difficulty, and security economics (PoW)
- Target difficulty is a threshold: a valid block hash must be numerically lower than the target.
- If more total hash power joins, blocks would arrive faster. Networks periodically adjust difficulty so block intervals stay near the target (e.g., ~10 minutes for Bitcoin).
- Security emerges from cost: rewriting history requires redoing work at or above the honest network’s cumulative hash power. That’s economically prohibitive for deep reorgs.
Common misconceptions
- “Hashes are encryption” — No. A hash is not reversible. It proves integrity; it does not hide data.
- “If two inputs have the same hash, the function is broken” — A single engineered collision in a lab setting does not necessarily break all use cases. Practical impact depends on context. Still, avoid algorithms with known practical collision attacks (e.g., MD5, SHA-1).
- “Proof of Stake doesn’t need hashing” — It does, for commitments, state roots, proofs, and randomness.
Quantum computing and hashing
Quantum algorithms change some security margins:
– Grover’s algorithm provides a quadratic speedup for brute-force preimage search, effectively making an n-bit hash behave like n/2 bits for preimage. For 256-bit functions, that’s still enormous.
– Doubling output size is a common hedge. Today’s mainstream 256-bit hashes remain comfortable.
Choosing a hash function for your dApp or protocol
- Use a battle-tested function: SHA-256, SHA-3/Keccak-256, or BLAKE2/3 depending on ecosystem norms and tooling.
- Consider interoperability: Ethereum tooling expects keccak-256; Bitcoin data commonly uses SHA-256.
- Apply domain separation: include clear prefixes like “myapp:v1:” before hashing to segregate different message types.
- Hash exactly what you mean: serialize data consistently (RLP, protobuf, CBOR) before hashing.
Practical checklist for working with hashes
- Always encode and serialize consistently. Ambiguous encodings lead to mismatched hashes.
- Be mindful of byte order (endianness) in Bitcoin vs display formats.
- Never compare raw strings when you mean to compare hashes; compute and compare digests.
- Use constant-time comparisons for secret-adjacent operations.
- Don’t mix password hashing with general-purpose hashing—use Argon2 or scrypt for passwords.
Hands-on mini lab: inspect a transaction hash
1) Create or obtain a small on-chain transaction on Bitcoin or Ethereum.
2) Copy the transaction hash (txid / transaction hash) into a block explorer.
3) Inspect fields: gas used (ETH), confirmations, block number, and the Merkle/receipt tree context. Notice how the hash acts as the canonical reference.
Want to try this with real assets? A regulated exchange with solid tooling makes it easy to fund a wallet, withdraw to self-custody, and inspect the resulting tx hash on-chain.
- Get started with OKX and use referral code CRYPTONEWER when you sign up. Fund an account, buy a small amount of crypto, and withdraw to your wallet to generate a live transaction hash you can explore. The interface is beginner-friendly and the fees are competitive for test-size transfers.
Developer corner: hashing in smart contracts
- Solidity
- keccak256(bytes) is the workhorse for unique IDs and mapping keys.
- EIP-712 uses structured data hashing to make signatures user-readable and unambiguous.
- Gas considerations
- Hashing small inputs is cheap, but iterative hashing in loops can be expensive. Batch off-chain when feasible and pass the Merkle root on-chain.
- Verifiable data
- Commit to data via on-chain hashes; reveal off-chain later with proofs for efficient verification.
Frequently asked questions
What Is Hashing in Blockchain?
It’s the process of using a cryptographic hash function to convert data into a fixed-length fingerprint. Blockchains use these fingerprints to link blocks, identify transactions, and verify inclusion via Merkle trees.
Can a hash be reversed?
No—good cryptographic hashes are designed to be one-way. Finding an input that maps to a given hash (preimage) should be computationally infeasible.
What if two inputs produce the same hash?
That’s a collision. For secure hash functions with 256-bit outputs, finding a collision by brute force is astronomically hard. If a function suffers practical collision attacks (like MD5), don’t use it.
Why do miners hash so much in Proof of Work?
They’re searching for a block header whose hash is below the difficulty target. Because outputs are unpredictable, the only approach is massive parallel trial-and-error.
Is SHA-256 broken?
No. SHA-256 remains widely trusted with no known practical collisions. SHA-1 and MD5 are considered broken for collision resistance and should be avoided.
Is Ethereum’s keccak-256 the same as SHA-3?
Close, but not identical. Ethereum uses the pre-standardization keccak variant; FIPS 202 standardized SHA-3 with different padding. In practice, use the function your ecosystem expects.
How big is a hash?
Commonly 256 bits (32 bytes), displayed as a 64-character hexadecimal string. Other lengths (e.g., 160, 224, 384, 512 bits) exist.
Where do I see a hash as a user?
- Transaction hashes in explorers (e.g., Etherscan, mempool.space)
- Block hashes
- Contract addresses derived from public keys
How can I experience hashing firsthand?
Move a small amount of crypto on-chain, then paste the transaction hash into a block explorer to see confirmations and inclusion proofs. If you need a place to start, sign up at OKX with the referral code CRYPTONEWER, fund a small balance, and withdraw to your wallet to generate a live tx hash.
Resources and further reading
- Bitcoin whitepaper: Satoshi Nakamoto (2008)
- Ethereum developers: Hash functions
- NIST: SHA-3 standard
- BLAKE family: BLAKE2 website and BLAKE3
Try it today with OKX
- Create your account at OKX
- Enter referral code: CRYPTONEWER
- Buy a small amount of crypto and withdraw to your wallet
- Paste the resulting transaction hash into an explorer to see hashing at work
Hashing may feel abstract until you see it power a real transaction. Once you do, “What is hashing in blockchain?” turns from a theory question into something you can actually observe and verify in seconds.